Network Security: Types and importance

Network security is impossible to overestimate the significance of in a technologically driven world. Network security is essential, regardless of whether you’re a user worried about your personal information or a business owner protecting valuable data. We’ll take you through all the fundamentals of network security in this post, from comprehending the fundamentals to putting best practices into practice and staying current with emerging trends.
Table of Contents
ToggleWhat is network security?

A collection of technologies known as network security guards against a wide range of possible dangers from entering a network or spreading throughout it, preserving the functionality and integrity of an organization’s infrastructure.
Tools for safeguarding both the network and the apps that use it make up a network security architecture. Multiple automated and scalable lines of defense are used in effective network security strategies. An administrator-determined set of security policies is enforced by each protective layer.
Types of Network Security Protections
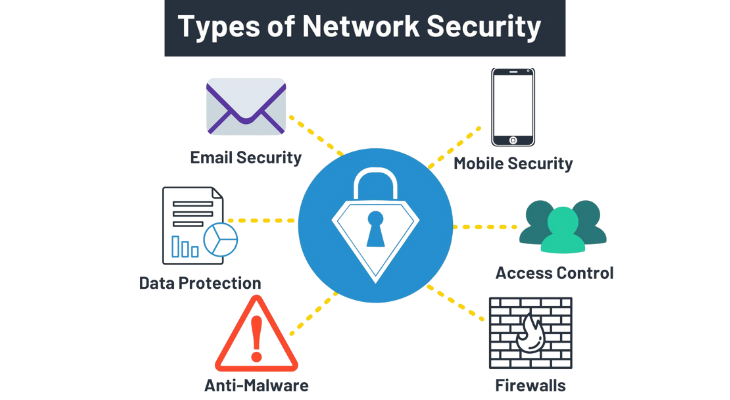
- Firewall:Firewalls are an essential component of everyday computing since they filter out malicious communications. Firewalls play a major role in network security, particularly Next Generation Firewalls, which concentrate on thwarting malware and application-layer attacks.
- Network Segmentation:When assets in a group share a function, risk, or role within an organization, those segments’ boundaries are defined by network segmentation. The perimeter gateway, for example, divides an organization’s network from the Internet. Sensitive information belonging to an organization is kept inside by thwarting any outside threats. To enhance security and control over access, organizations might further develop their network by drawing extra internal borders.
- What is Access Control?In order to prevent unauthorized access and potential dangers, access control restricts the individuals, organizations, and devices that are allowed to use network applications and services. Role-based Access Control (RBAC) regulations make ensuring the person and device have permission to access the asset, and integrations with Identity and Access Management (IAM) products can help to strongly identify the user.
- Remote Access VPN:Remote access VPN enables individual hosts or customers, including telecommuters, mobile users, and extranet consumers, to have secure remote access to a company network. Usually, each host utilizes a web-based client or has VPN client software loaded. Encryption of all transferred data, endpoint compliance scanning, and multi-factor authentication guarantee the privacy and integrity of sensitive information.
- Access to Zero Trust Networks (ZTNA):According to the zero trust security paradigm, a user should only be granted the access and authorization necessary for them to carry out their duties. Compared to standard security solutions, such as VPNs, which give users complete access to the target network, this is a fundamentally different approach. Software-defined perimeter (SDP) solutions, sometimes referred to as zero trust network access (ZTNA), allow people who need that access to carry out their job responsibilities to have specific access to an organization’s applications.
- Email Security:Any procedures, goods, and services intended to keep your email accounts and content safe from outside threats are referred to as email security. Although the built-in email security mechanisms of the majority of email service providers are intended to keep you safe, they might not be sufficient to prevent hackers from accessing your data.
- Data Loss Prevention (DLP):In order to prevent sensitive information from being exposed outside of an organization, particularly regulated data like personally identifiable information (PII) and compliance-related data like HIPAA, SOX, PCI DSS, etc., data loss prevention, or DLP, is a cybersecurity methodology that combines technology and best practices.
- Intrusion Prevention Systems (IPS):Network security threats like brute force attacks, Denial of Service (DoS) attacks, and exploits of known vulnerabilities can be identified or stopped by IPS systems. An exploit is an assault that takes advantage of a vulnerability, such as a weakness in a software system, to take control of the system. Attackers frequently have a window of opportunity to take advantage of a vulnerability once it is made public before the security patch is implemented. In these situations, an intrusion prevention system can be employed to swiftly stop these attacks.
- Sandboxing:Sandboxing is a cybersecurity technique in which files are opened or code is performed on a host computer that simulates end-user operating environments in a secure, isolated environment. To keep threats off the network, sandboxing watches the code or files as they are opened and searches for harmful activity. Before the files reach an unwary end user, malware, for instance, can be safely recognized and prevented in formats like PDF, Microsoft Word, Excel, and PowerPoint.
- Hyperscale Network Security:The ability of an architecture to adapt when more demand is placed on the system is known as hyperscale. This system may be quickly deployed and scaled up or down in response to shifting network security requirements. All of the hardware resources in a clustering solution can be fully utilized by tightly integrating networking and compute resources in a software-defined system.
- Cloud Network Security:Workloads and applications are no longer only housed in a nearby data center on-site. More adaptability and creativity are needed to protect the modern data center as application workloads move to the cloud. In private, public, hybrid, and cloud-hosted Firewall-as-a-Service (FWaaS) deployments, network security solutions are made possible by software-defined networking (SDN) and software-defined wide area network (SD-WAN) solutions.
Why is network security important?
Network security is essential because it keeps sensitive and valuable data from being obtained by cybercriminals. Such data can be taken by hackers, who then use it to commit identity theft, asset theft, and reputational damage, among other crimes.
Four important explanations for the significance of network and data protection are as follows:
- Operational risks. An organization runs the danger of having its operations disrupted by inadequate network security. Networks, both personal and business, rely on hardware and software that are inoperable in the presence of malware, viruses, and cyberattacks. Networks are also necessary for most internal and external business communication.
- Financial hazards associated with personally identifiable information (PII) compromise. For both people and companies, data breaches may be costly. Organizations that handle personally identifiable information (PII) must protect it, including passwords and Social Security numbers. The victims may have to pay for hacked equipment to be repaired, fines, and reparations after being exposed. Additionally, exposure to significant data breaches can destroy a company’s brand and put it in legal hot water. The average cost of a data breach increased to $4.35 million in 2022 from $4.24 million in 2021, according to IBM’s “Cost of a Data Breach 2022 Report,” which was carried out by Ponemon Institute.
- Risk to finances due to stolen intellectual property. It is also possible for organizations to lose money due to intellectual property theft. A corporation may lose sales and its competitive edge if its concepts, inventions, and products are lost.
- Lawful matters. Numerous nations mandate that companies abide by data security laws that address various facets of network security. For instance, medical institutions operating in the United States must abide by the Health Insurance Portability and Accountability Act (HIPAA), and entities operating in the European Union that handle the data of their residents must abide by the General Data Protection Regulation (GDPR). Breaking these rules may result in penalties, prohibitions, and even jail time.
- Because network security is so crucial, many firms concentrate on implementing and exchanging tactics for fending off contemporary dangers. In order to provide cyber threat intelligence and assist companies and other organizations in assessing their network security practices, Mitre ATT&CK, the National Institute of Standards and Technology, and the Center for Internet Security offer free, nonproprietary security frameworks and knowledge bases.
How does network security work?
Hardware and software tools are combined to enforce network security. Network security’s main objective is to stop illegal access to or from within a network’s components.
An organization’s network security and compliance with security standards and laws are determined by a security official or team through the development of strategies and policies. These security guidelines must be followed by every user on the network. Any place on the network where a legitimate user could access data is also a potential entry point for malevolent actors or negligent or mistaken users to compromise data.
Network security benefits

The ability of a company to provide goods and services to clients and staff depends on network security. Protecting networked apps and data is crucial for business advancement and reputation management, especially when it comes to online storefronts, enterprise programs, and remote desktops. In addition, by removing downtime brought on by successful attacks, efficient network security can enhance network performance.
What are the key tools of network security?

In order to provide thorough access control and threat control, a multi-layered approach to network security applies controls at multiple locations inside a network.
- Firewall: A firewall creates a wall on a network between trustworthy and untrusted parts. As a result, a firewall uses IP subnets to carry out macro-segmentation and access control. Additionally, the same firewall may carry out micro-segmentation, which is segmentation at a finer level.
- A load balancer is a device that distributes load according to metrics. Beyond basic load balancing, a load balancer can provide the ability to absorb certain attacks, such a volumetric DDoS attack, by putting specific mitigation measures into practice.
- IDS/IPS: The traditional IDS/IPS offers protocol analysis and signature matching on different portions of a data packet and is implemented behind a firewall. Protocol analysis is a means of verifying conformance with the protocol’s publicly published specification. By matching signatures, known threats like SQL injection are thwarted.
- Sandbox: An IDS/IPS and a sandbox are comparable in that they don’t rely on signatures. For example, a sandbox can simulate an end-system environment and detect whether an object of malware is attempting to perform port scans.
- NTA/NDR: NTA/NDR examines traffic directly, or traffic records like NetFlow, and use statistical methods and machine learning algorithms to assess anomalies and identify potential threats. NTA/NDR starts by attempting to establish a baseline. Once a baseline is established, abnormalities like traffic spikes or sporadic communication are detected.
Emerging Trends in Network Security
Network security dangers and problems are always changing in tandem with technology. It is crucial to keep up with these new developments if you want to protect your digital assets. The following are some significant developments to be mindful of:
1. Machine learning and artificial intelligence (AI/ML)
In the battle against cyber threats, artificial intelligence (AI) and machine learning (ML) have assumed a central role. With the use of these technologies, security systems can now analyze enormous volumes of data in real-time and are better equipped than ever to spot anomalies and possible threats. Additionally, AI/ML can adjust to novel and changing threats, strengthening your network’s overall security posture.
How It Affects You: You may better defend your network against sophisticated threats that could otherwise go undetected by utilizing security technologies driven by AI and ML. By promptly recognizing and reacting to anomalous behaviors and trends, these technologies mitigate the danger of sensitive information leaks.
2. Security of the Internet of Things (IoT)
Network security issues now take on a new dimension as a result of the widespread use of IoT devices. Smart home appliances and industrial sensors are only two examples of IoT devices that frequently lack strong security features. They can therefore act as access points into your network and become exposed to attacks. It’s getting more and more crucial to secure Internet of Things devices and control how they interact with your network.
How It Affects You: You must exercise caution when it comes to IoT security. To avoid potential security breaches and unauthorized access, make sure all linked devices are up to date on security upgrades and are configured correctly.
3. Cloud Security
The transition to cloud-based storage and services has completely changed how businesses run. The cloud has numerous benefits, but it also raises special security issues. Compared to on-premises solutions, ensuring the security of data and applications in the cloud calls for a different strategy.
How It Affects You: It’s Important to comprehend the shared responsibility model with cloud service providers as more of your digital assets are moved to the cloud. In the cloud environment, you must secure data protection, monitor for potential risks, and implement the appropriate security policies.
4. Zero Trust Security Model
The conventional paradigm for network security made the assumption that everything inside the network could be trusted, but outside sources could not. The Zero Trust paradigm, however, casts doubt on this presumption. Every person and device, whether inside or outside the network, must be verified and authorized before accessing resources. This is done in accordance with the motto, “never trust, always verify.”
How It Affects You: Putting the Zero Trust paradigm into practice necessitates a major revision to your network security strategy. To maintain a high level of security, rigorous access controls, vigilant identity management, and ongoing monitoring are necessary.
5. Quantum Computing Threats
Quantum computing presents a danger to existing encryption techniques even as it has the potential to lead to revolutionary advancements. Existing encryption systems may be broken by quantum computers, leaving data accessible. One of the main concerns for the future is becoming ready for the emergence of encryption techniques resistant to quantum computing.
How It Affects You: Keep up with developments in quantum computing and be prepared to safeguard your data by implementing post-quantum encryption techniques as soon as they become accessible.
Conclusion
We’ve covered the principles, best practices, new trends, key tools, and practical examples of network security in this extensive book. Through adherence to these recommendations, ongoing education, and proactive measures, you may greatly improve network security and safeguard your digital environment from possible dangers.
Recall that maintaining network security is a continuous endeavor. To keep your data and digital assets safe, you need to be knowledgeable and on guard. Maintaining the security of your network requires ongoing dedication to safeguarding the things that are most important.
Network Security FAQs
What Are Common Network Security Threats?
Distributed Denial of Service (DDoS) assaults, malware, and phishing scams are examples of common threats to network security. Every hazard is different and calls for a different set of precautions.
What Are Some Ways to Protect My Network From Malware?
Installing dependable antivirus software, keeping it updated, and warning users about the dangers of downloading files from untrusted sources are all necessary steps in protecting your network from infection.
What Role Does a VPN Play in Network Security?
A private and secure internet connection is guaranteed by a virtual private network, or VPN. Your data is encrypted, making it more difficult for someone to intercept or keep an eye on your online activity.




One Comment