Virtual Private Networks (VPN )Basics: Secure Internet Connection
VPN is more important than ever to protect your online presence in the connected digital world of today. VPNs, or virtual private networks, have become a reliable friend in the fight against cybercrime and privacy. You’ve come to the correct place if you’ve been wondering what a VPN is, how it operates, and why you might need one. This post will guide you through the nuances of virtual private networks (VPNs), addressing your inquiries and offering insightful analysis to support your decision-making.
Table of Contents
ToggleDemystifying VPN Technology
What is a VPN?
Let’s define VPN first before getting into the specifics. The acronym VPN stands for “Virtual Private Network.” It functions similarly to a private, encrypted internet channel that lets you send data without being tracked by prying eyes.
How VPNs Work
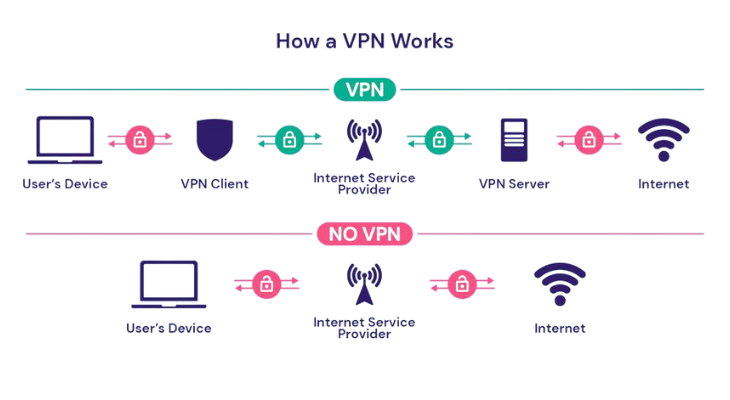
Data security and encryption are essential to a VPN’s operation. VPNs protect your data from any possible eavesdroppers by using strong encryption techniques. Your information is transformed into a code that can only be read by the designated recipient.
VPNs also use IP address masking and tunneling to give users anonymity. This implies that not only is your data safe, but also that your true identity and whereabouts are hidden.
Understanding VPN Types
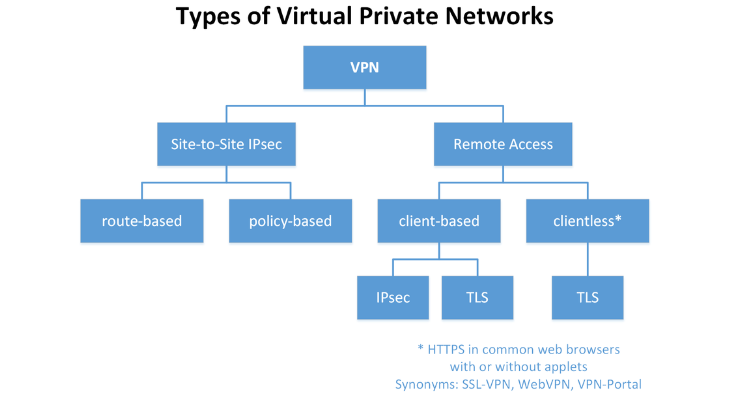
There are several varieties of VPN technology, each meeting a different set of requirements. First, let’s examine the two main kinds:
1. Remote Access VPN
Your key to safely establishing a remote connection to a private network is a remote access virtual private network, sometimes known as a “Secure Remote Access” solution. With the protection required for private business duties, this kind is a lifesaver for distant workers.
A Remote Access VPN, for instance, is the solution if you’ve ever pondered how to safely access your business server from your home computer. It lets you work from a distance without jeopardizing the security of private information.
2.Site-to-Site VPN
Between Sites VPNs operate similarly to virtual bridges, securely bridging disparate networks—for example, branch offices and central headquarters. These networks work together as a single, coherent system, facilitating smooth and secure data sharing and communication.
Site-to-Site VPNs are what you need if your company has several locations and you need them all to function together. They make sure that information moves between the various branches securely and effectively.
What is a VPN Used For?
After dispelling the myths around the technology, let’s examine some practical uses for it.
Business and Corporate Use
Virtual private networks, or VPNs, are the defenders of business data privacy. They make it possible for companies to exchange private data securely over networks. This is especially helpful for distant teams that want access to private company information.
VPNs protect your company’s data from prying eyes, even when it is shared across international borders.
Personal Use
VPNs provide a private online barrier for individuals. Are you concerned about who might be keeping an eye on your internet activity? Your virtual veil of invisibility is a VPN. It’s the ideal tool for protecting your security and privacy when you browse the internet.
A VPN makes sure that your online presence stays your business, whether you’re at home, in the office, or at an airport.
VPN Benefits

Anonymity and Privacy
A VPN is your protector when it comes to your valuable online anonymity. It makes sure that no one else can see what you do online by hiding your IP address and encrypting your data. Given the prevalence of online surveillance in today’s environment, privacy is increasingly important.
Security and Data Protection
VPNs serve as a barrier against hackers and data breaches in a time when there are a lot of cyber risks. They guard against such cyberthreats by promising that your private information will stay private.
Risks and Concerns
Although VPNs provide strong protection, there are a few things to keep in mind.
VPN Logging and Privacy Risks
Your online activity may be recorded by certain VPN providers. Selecting a supplier with a stringent no-logs policy is essential to guaranteeing that your privacy is protected.
VPN Speed and Performance
Your internet speed may be slightly slower when using a VPN because of the encryption procedure. By choosing a top-notch VPN provider, you can lessen this problem and have a more seamless online experience.
Disadvantages or drawbacks of using a VPN
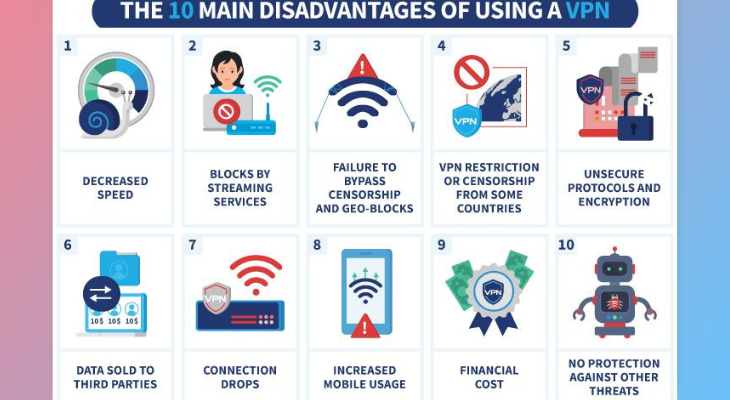
- Limited Server Access: In instance, free VPNs might only offer a small number of servers and locations. Reduced performance and crowding may result from this.
- Access Denied: A few websites and online services proactively prevent users from connecting via VPN. This is particularly prevalent with streaming services, which makes it difficult to get geo-restricted content.
- Security Issues: Virtual private networks (VPNs) are intended to improve security, however not all VPN service providers are reliable. Some might log your information or use shoddy encryption, which puts your privacy at risk.
- Incompatibility: When a VPN is in use, some programs and services might not function properly. This may be because the VPN’s IP addresses are blocked or because the provider has restrictions in place.
- Legal and Policy Concerns: Using a VPN for illicit purposes is still prohibited in some nations, and using one for private purposes is banned in others. Understanding the rules and regulations in your area is crucial.
- Reliability: A VPN service’s dependability can differ. Your internet access may be interrupted if there is an outage or technical issue with the VPN server.
- Overhead: The encryption and decryption operations that VPNs involve can cause your device to become more unresponsive and shorten the life of its battery on mobile devices.
- Data Privacy Concerns: Although VPNs shield your information from your ISP, they still require some degree of faith in the VPN service provider. You have to have faith that the VPN service will manage your data sensibly.
- Limited Customer service: Some free VPNs might not have strong customer service, which makes it challenging to fix problems or obtain help when you need it.
VPN App for Free
- ProtonVPN: ProtonVPN is renowned for its steadfast dedication to security and privacy. Unlike other free VPNs, it provides unlimited bandwidth on its free package. It doesn’t show any advertisements and features an easy-to-use interface.
- Windscribe: Windscribe provides 10GB of data per month as part of a free package. It offers access to servers located across several nations and enjoys a solid reputation for privacy and security.
- TunnelBear: TunnelBear is renowned for both its robust user privacy protection policy and its intuitive design. 500MB of data is available each month with its free plan, which is plenty for sporadic use.
- Hotspot Shield: Hotspot Shield service offers a restricted number of servers and an ad-supported free plan. For simple surfing and streaming needs, it provides acceptable speed and performance.
- Hide.me: Hide.me offers a 2GB monthly data package that is free of charge. It is renowned for having robust privacy protections, such as a no-logs policy and effective security measures.
Steps for Using a VPN
Step 1: Data Encryption
Your data’s trip over a VPN starts with encryption. A VPN connection converts your data into unintelligible code. To make sure that even if someone intercepts your data, they won’t be able to interpret it, this method uses encryption techniques.
Using encryption ensures that only authorized parties may access your data, much like locking it in a safe digital vault. If you don’t have the encryption key, your data is kept secret from prying eyes.
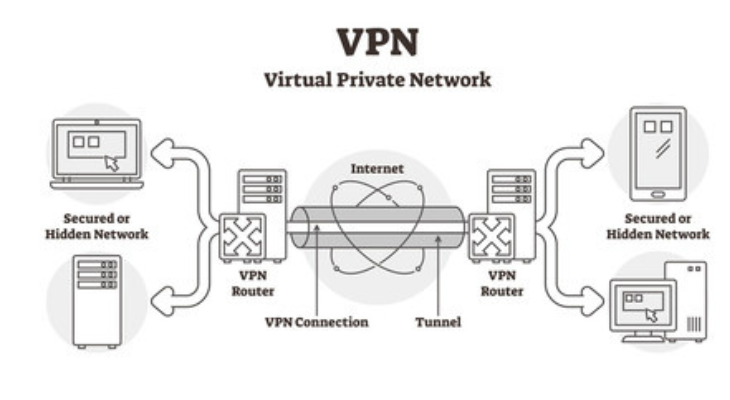
Step 2: Secure Connection Establishment
The VPN software creates a secure connection between your device and the VPN server after your data has been encrypted. Most people call this connection a “tunnel.” Your data passes across this virtual conduit on its journey to and from the internet.
To make sure that your data is safe while traveling over the expansive and possibly hazardous internet, a VPN tunnel is essential. For your data, it functions similarly to a private road in a world of public highways.
Step 3: IP Address Masking
Similar to a digital fingerprint, an IP address enables you to associate your online activities with a particular internet-connected equipment. A VPN, on the other hand, hides your IP address. The VPN replaces your real IP address with a new one based on the server’s location.
This IP address masking not only protects your online privacy but also lets you access material and websites that could be prohibited locally. Because it looks that you are browsing from the VPN server’s location, you unlock a world of possibilities.
Step 4: Transfer of Data
Once your IP address has been disguised, a secure connection has been established, and your data has been encrypted, it is ready for transfer. Data transmitted or received via the internet travels via the virtual private network (VPN) and reaches the VPN server.
At the VPN server, your data is decrypted before being sent to its online location. The request seems to be coming from the VPN server rather than your device on the website or online service you are viewing. This ensures that your actual whereabouts and identity remain a secret.
Step 5: Data Return and Re-Encryption
The data returns to the VPN server first when the website or online service answers to your query. It is encrypted at the server and then delivered back to your device via a secure tunnel.
The data is encrypted when it reaches your device, allowing you to read and access it. The security of your data is guaranteed during the whole connection cycle thanks to this two-way encryption and decryption procedure.
Step 6: Secure Data Reception
The decrypted data can then be viewed and used on your device as required. The data is handled as though it were sent straight to your device, regardless of whether you are reading an email, downloading a file, or viewing a webpage.
A secure and private online experience is provided by the quick and flawless completion of the entire procedure, which includes data encryption and secure receiving.
Conclusion
Finally, in an increasingly linked online world, virtual private networks, or VPNs, are your pals in the digital realm, providing security, privacy, and protection. Knowing their advantages and how they operate gives you the power to make wise decisions about protecting your digital life. You can traverse the digital terrain with assurance when you have a trustworthy VPN at your side, knowing that your privacy and data are secure.
FAQs about VPN
Is it legal to use a VPN?
In most countries, using a VPN for legitimate purposes, such as privacy and security, is legal. However, using a VPN for illegal activities remains illegal, regardless of the technology’s use.
Are all VPNs the same?
No, VPNs can vary significantly in terms of features, security, speed, and the level of privacy protection they offer. It’s essential to choose a reputable VPN provider based on your specific needs.
Do I need to pay for a VPN?
Paid VPN services generally offer better performance, more features, and higher security. Your choice depends on your requirements and budget.
Can a VPN hide my online activities from my ISP?
Yes, a VPN can encrypt your internet traffic, making it difficult for your Internet Service Provider (ISP) to monitor your online activities. However, your ISP will still be aware that you are using a VPN.
Can I use a VPN on my mobile device?
Yes, most VPN services offer apps for various platforms, including smartphones and tablets, making it easy to use a VPN on your mobile device.
Can I use a VPN to access streaming services in other countries?
Yes, a VPN can help you access geo-restricted content on streaming platforms by connecting to a server in the desired location.
Are there any risks to using a VPN?
While VPNs enhance privacy and security, it’s crucial to choose a reputable provider. Using a poorly configured or malicious VPN can potentially expose you to risks. Always research and choose a trusted VPN service.




One Comment